The Role of the OSI Model in Modern Process Control Systems
The Open Systems Interconnection (OSI) model is a conceptual framework used to understand and implement networking protocols in seven layers. In process control in engineering, the OSI model plays a crucial role in ensuring reliable, efficient, and secure communication between various components of a control system, from sensors and actuators to controllers and human-machine interfaces.
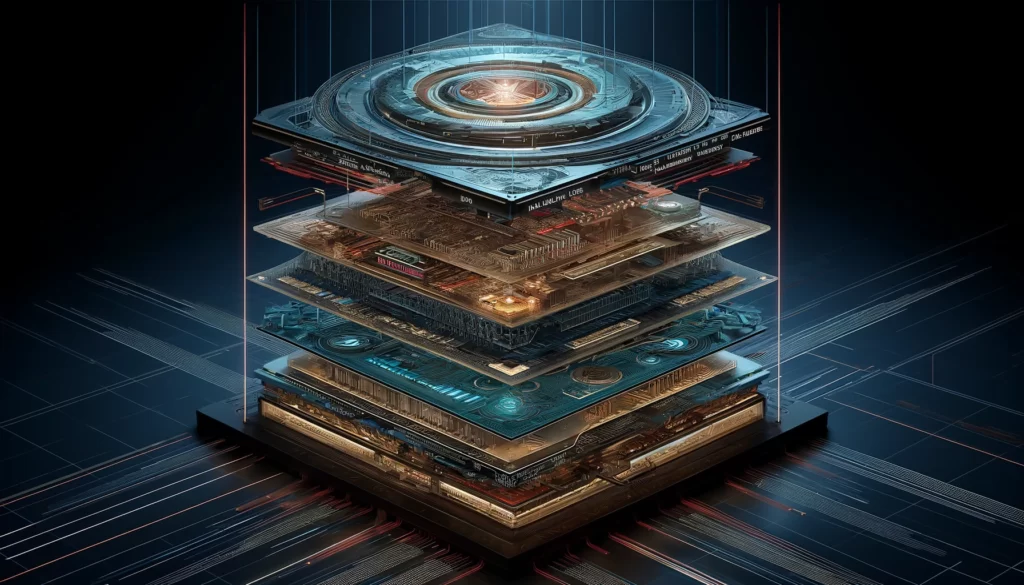
The OSI model’s seven layers – Physical, Data Link, Network, Transport, Session, Presentation, and Application – each serve a unique function in the data communication process. For engineering process control, understanding and applying these layers correctly is vital for the seamless operation of control systems.
At the Physical layer, the model deals with the actual physical connection between devices, including cables, switches, and other hardware. This is fundamental in a process control environment where robust and reliable hardware connections are necessary for accurate data collection and actuation.
The Data Link layer ensures that data frames are transmitted without errors between two nodes connected by the physical layer. In process control, this layer helps in error detection and correction which is crucial for maintaining the integrity of control signals.
The Network layer is responsible for data transmission between different networks. This is essential in complex control systems that may span different network segments, ensuring that data packets are routed correctly between devices.
The Transport layer provides reliable data transfer services to the upper layers. This includes flow control, error handling, and data segmentation. In process control systems, this layer ensures that control commands and sensor data are transmitted reliably, maintaining system stability and performance.
The Session layer establishes, manages, and terminates connections between applications. This is important in process control for managing sessions between control systems and remote operators or between different control systems.
The Presentation layer translates data between the application layer and the lower layers, ensuring that data is in the correct format. In process control, this could involve the translation of data from sensors into a format understandable by control algorithms.
Finally, the Application layer provides the interface for end-users and applications to access network services. This layer is where operators interact with the control system, inputting commands and receiving feedback.
How Profinet and Scada relate to the OSI model
Profinet and SCADA (Supervisory Control and Data Acquisition) systems are integral components of modern industrial automation and control processes, and both relate to the OSI model in how they communicate and manage data across a network.
Profinet
Profinet is an industry technical standard for data communication over Industrial Ethernet, designed for collecting data from and controlling, equipment in industrial systems. It is built on the Ethernet standard and thus inherently uses the lower layers of the OSI model:
- Physical Layer: Profinet uses standard Ethernet physical layer technologies, including copper and fibre optic cables, to connect devices.
- Data Link Layer: Profinet operates here by utilising Ethernet frames for device-to-device communication, ensuring data is packaged and addressed correctly for devices on the network.
- Network Layer: While traditional Ethernet doesn’t inherently fit into the OSI model’s Network layer (as it’s primarily a Layer 2 technology), Profinet uses IP protocols when integrating with broader networks, thus engaging with Layer 3 functionalities for routing and addressing across network boundaries.
Profinet integrates seamlessly with TCP/IP (which spans the Transport and Network layers of the OSI model) for non-time-critical communication and reserves the lower layers (especially the Data Link layer) for real-time communication crucial in process control.
SCADA
SCADA systems are used for monitoring and controlling industrial processes at a high level. They are typically composed of a central control system that communicates with remote terminal units (RTUs) and programmable logic controllers (PLCs) to control field devices. SCADA systems interact with the OSI model in various layers:
- Data Link and Physical Layers: Similar to Profinet, SCADA systems use these layers for the physical connection and data framing between devices in the field and the central control system.
- Network Layer: SCADA systems may use IP protocols to route messages across different networks, especially in distributed installations where components are geographically dispersed.
- Transport Layer: SCADA often utilises TCP or UDP (part of the TCP/IP suite, which corresponds to the OSI’s Transport layer) to ensure reliable data transmission or more straightforward, connectionless communication.
- Application Layer: SCADA interfaces, where operators interact with the system, operate at this layer, providing the necessary protocols for data access, visualisation, and control.
Both Profinet and SCADA systems demonstrate the practical application of the OSI model’s layers in industrial environments. They use the model’s lower layers (Physical, Data Link, and sometimes Network) for the essential, real-time communication needed in process control, while also engaging higher layers (Transport and Application) for broader system integration, data management, and user interaction. This layered approach facilitates interoperability, standardisation, and reliability in complex industrial control systems.
Theory behind the OSI Model for Engineers
The Open Systems Interconnection (OSI) model, established by the International Organisation for Standardisation (ISO), is founded on several core engineering principles and theories that facilitate the understanding, development, and implementation of network systems. These principles include abstraction, encapsulation, modularity, and layering, which together contribute to the model’s robust framework for network communication.
Abstraction
Abstraction in the OSI model allows network engineers and developers to focus on the functionality of each layer without needing to understand the detailed workings of the other layers. This principle simplifies network design and troubleshooting by abstracting the complexities of network communications into manageable, discrete layers.
Encapsulation
Encapsulation refers to the method of taking data from a higher layer and adding a header (and sometimes a footer) to it at the next layer down. This process allows each layer to add the necessary control information to ensure proper data transmission and interpretation. For instance, data at the Transport layer is encapsulated with a header containing port numbers before being passed down to the Network layer.
Modularity
The OSI model’s modularity means that each layer is designed to perform a specific, independent function. Changes or improvements can be made to one layer without affecting the others, provided the interface between the layers remains unchanged. This principle supports scalability and adaptability in network architectures, allowing new technologies and protocols to be integrated seamlessly into existing systems.
Layering
Layering is the foundation of the OSI model, dividing the complex process of network communication into seven distinct layers. Each layer serves a specific purpose and communicates with the layers directly above and below it. This hierarchical organisation ensures that specific tasks related to network communication are compartmentalised, making the system easier to understand, develop, and maintain.
Interoperability and Standardisation
The OSI model promotes interoperability and standardisation across different systems and technologies by providing a universal set of rules and protocols. By adhering to these standards, different network devices and software can communicate effectively, regardless of their underlying architecture or vendor.
Error Handling and Data Flow Control
The OSI model incorporates mechanisms for error detection and correction, particularly at the Data Link and Transport layers. This ensures that data integrity is maintained across the network. Similarly, flow control mechanisms prevent network congestion by regulating the amount of data sent between devices, ensuring that the receiver can adequately process the incoming data.
Security
Security considerations are integrated into various layers of the OSI model, with specific protocols designed to address security concerns such as authentication, data integrity, and encryption. For example, the Application layer includes protocols with built-in security features for secure data transmission over the Internet.
In essence, the OSI model’s engineering principles and theoretical foundations facilitate a structured approach to network design and communication. By adhering to these principles, the model provides a framework that supports the development of interoperable, scalable, and robust network systems.

Enhancing Process Efficiency: OSI Model in Action
To illustrate the real-world application of the OSI model in engineering, let’s consider the deployment of a smart manufacturing system, an integral part of Industry 4.0. This example will demonstrate how each layer of the OSI model plays a vital role in ensuring seamless communication and operation within a complex, interconnected system.
Scenario: Smart Manufacturing System
A smart manufacturing system integrates various technologies such as IoT (Internet of Things) devices, AI (Artificial Intelligence), and robotics to create a highly efficient, automated production environment. These technologies rely on robust network communication to interact with each other and with centralised control systems.
Application of OSI Model Layers
1. Physical Layer:
The foundation of our network involves the physical setup, including Ethernet cables, Wi-Fi routers, and switches that connect different devices like sensors, actuators, and control units within the factory. This layer ensures the transmission of raw bit streams over these physical mediums.
2. Data Link Layer:
This layer manages the communication between devices on the same network. In our factory, this might involve Ethernet protocols that organise data into frames and control access to the network media, ensuring that devices like robotic arms receive the correct commands without interference.
3. Network Layer:
With multiple networks within the factory, such as separate systems for assembly, quality control, and inventory management, the Network layer is responsible for routing data packets between these networks. This could involve using IP addresses to ensure that data from IoT sensors in the assembly line reaches the central control system for processing.
4. Transport Layer:
This layer ensures reliable data transfer between end systems. For instance, a monitoring system that analyses the real-time performance of assembly robots might use TCP (Transmission Control Protocol) to ensure that all data packets arrive in order and without errors.
5. Session Layer:
This layer establishes, maintains, and terminates sessions. In our scenario, when an operator uses a control panel to configure a machine or run diagnostics, the Session layer manages these interactions, ensuring that each session is kept separate and secure.
6. Presentation Layer:
Data from various sources in the factory needs to be translated into a format that the receiving application can understand. For example, data from sensors might be encoded in different formats; the Presentation layer ensures it’s converted into a standard format before it’s processed or displayed on the control systems.
7. Application Layer:
At the top of the OSI model, this layer provides the interface for end-users and applications. In the smart manufacturing system, this could involve interfaces for monitoring production metrics, systems for managing inventory based on real-time data, and applications for predictive maintenance.
In this smart manufacturing scenario, the OSI model provides a structured framework for managing the complex communications required to operate the system efficiently. By compartmentalising network functions into specific layers, the model facilitates troubleshooting, scalability, and integration of new technologies, ensuring that the smart factory can adapt to new demands and technologies over time. This example underscores the relevance of the OSI model in designing and managing modern, interconnected engineering systems.

Safeguarding Process Controls through the OSI Model
When utilising the OSI model for process control in industrial environments, security considerations are paramount, especially given the potential impact of security breaches on safety, productivity, and data integrity. Furthermore, white hat testing using tools like Kali Linux is an essential practice to identify vulnerabilities and strengthen the security posture of these systems. Below are key security considerations across different layers of the OSI model, along with how white hat testing can be employed:
Security Considerations by OSI Layer
Physical Layer:
- Unauthorised Access: Physical access to network devices can lead to unauthorised data access or system disruption. Measures like secure locking mechanisms for server rooms and network cabinets are essential.
- White Hat Testing: Regular audits and physical security assessments can identify potential vulnerabilities, ensuring that all physical components are adequately secured.
Data Link Layer:
- MAC Spoofing: Attackers may impersonate devices within the network by spoofing MAC addresses. Implementing port security on switches can mitigate this risk.
- White Hat Testing: Penetration testers can use tools to attempt MAC spoofing, assessing the network’s vulnerability to such attacks and the effectiveness of implemented defences.
Network Layer:
- IP Spoofing and DoS Attacks: IP spoofing can be used for identity masquerading, while DoS attacks can disrupt service. Firewalls and intrusion detection systems (IDS) can help mitigate these risks.
- White Hat Testing: Employing techniques like IP spoofing or simulated DoS attacks using Kali Linux tools can help test the resilience of the network against these threats.
Transport Layer:
- Session Hijacking: Attackers can take over web sessions. Solutions like SSL/TLS for encryption can secure data transmission.
- White Hat Testing: Tools in Kali Linux can simulate session hijacking attacks to test the effectiveness of encryption and session management security measures.
Session Layer:
- Session Management Vulnerabilities: Weak session management can lead to unauthorised access. Implementing strong session management practices is crucial.
- White Hat Testing: Testing for session management vulnerabilities, including session fixation and session prediction, can help in identifying potential weaknesses.
Presentation Layer:
- Data Encryption: Ensuring that data is appropriately encrypted before transmission can prevent data leakage. Utilising protocols like HTTPS is a standard practice.
- White Hat Testing: Analysing the encryption and data handling practices in use can help identify potential vulnerabilities or misconfigurations.
Application Layer:
- Application Vulnerabilities: Applications may have various vulnerabilities like SQL injection, Cross-Site Scripting (XSS), etc. Regular patching and secure coding practices are necessary.
- White Hat Testing: Using tools like Metasploit and OWASP ZAP from Kali Linux to conduct penetration testing and vulnerability assessments on applications can identify potential security flaws.
General Security Considerations
- Comprehensive Security Policy: Establishing and enforcing a robust security policy that covers all aspects of the network is crucial.
- Regular Updates and Patch Management: Keeping all software and firmware up to date is essential to protect against known vulnerabilities.
- Network Segmentation: Segregating the network can limit the spread of malicious activities and simplify the management of security policies.
- Employee Training: Regular training on security best practices can help prevent accidental breaches due to human error.
White Hat Testing with Kali Linux
Kali Linux is a powerful tool for white hat testing, offering a wide range of utilities specifically designed for security testing and ethical hacking. White hat testers can use Kali Linux to simulate various attacks on each OSI layer, identifying vulnerabilities before they can be exploited maliciously. It’s crucial that such testing is done systematically and with proper authorisation to ensure that it does not inadvertently disrupt operational systems.
In summary, understanding the security considerations of each OSI layer and employing thorough white hat testing practices are essential components of maintaining a secure process control environment. Regular testing, coupled with a strong security posture, can greatly reduce the risk of cyber threats in industrial control systems.

Penetration Testing: Safeguarding Profinet Systems
In the context of cybersecurity, the terms “white hat,” “grey hat,” and “black hat” refer to the intentions and ethics behind hacking activities. White hat hackers conduct ethical hacking to improve security, grey hat hackers operate in a legal and ethical grey area, often without explicit permission, and black hat hackers have malicious intent. When utilising the OSI model for process control, it’s essential to understand how these different approaches can impact system security and what considerations should be taken into account.
White Hat Testing
White hat testing involves authorised and ethical hacking to identify vulnerabilities and improve system security. In process control systems, white hat hackers systematically test each layer of the OSI model to uncover potential weaknesses.
- Authorisation: Ensure all testing is authorised by system owners to avoid legal and ethical issues.
- Comprehensive Testing: Test each OSI layer, focusing on specific vulnerabilities that might be present, from physical security at Layer 1 to application security at Layer 7.
- Documentation and Reporting: Document findings comprehensively and provide detailed reports to system administrators for remediation.
- Follow-up: After vulnerabilities have been addressed, conduct follow-up testing to ensure that fixes are effective and have not introduced new vulnerabilities.
Grey Hat Testing
Grey hat hackers might identify and sometimes exploit vulnerabilities without explicit permission but typically do not have malicious intent. They might notify the organisation of the vulnerability, sometimes expecting a bounty or recognition.
- Legal and Ethical Risks: Grey hat testing poses significant legal and ethical risks, as testing without permission is illegal in many jurisdictions and can result in unintended consequences.
- Unsolicited Testing: While grey hat hackers might uncover critical vulnerabilities, their unsolicited testing can disrupt operations and violate privacy and trust.
- Handling Grey Hat Disclosures: Organisations should have a clear policy for handling unsolicited vulnerability disclosures, including a possible bug bounty program to incentivise ethical reporting.
Black Hat Testing
Black hat testing is conducted with malicious intent, such as stealing sensitive data, disrupting operations, or gaining unauthorised access to systems.
- Threat Awareness: Understand the tactics, techniques, and procedures (TTPs) used by black hat hackers to better defend against them.
- Proactive Defense: Implement proactive security measures, including intrusion detection systems (IDS), regular penetration testing, and employee training to recognise phishing attempts and other common attack vectors.
- Incident Response Plan: Have a robust incident response plan in place to quickly and effectively respond to security breaches.
Considerations Across All Hats
- Layer-Specific Security: Each OSI layer has its own set of vulnerabilities and requires specific security measures. For example, encryption is crucial at the Transport layer, while strong authentication and access controls are vital at the Application layer.
- Holistic Security Approach: A comprehensive security strategy that covers all layers of the OSI model and aspects of organisational security (physical, technical, administrative) is essential.
- Continuous Monitoring and Improvement: Cybersecurity is an ongoing process. Continuous monitoring, regular updates, and adapting to emerging threats are critical for maintaining security.
Understanding the different perspectives and methodologies of white, grey, and black hat hackers can provide valuable insights into securing process control systems. Organisations must adopt a proactive and comprehensive security strategy that addresses potential vulnerabilities at each layer of the OSI model and prepares for the ethical and legal challenges associated with different types of hacking activities.

Navigating Profinet Troubles: Strategies and Tools for Effective Diagnosis
In the world of industrial network communications, Profinet stands out as a pivotal protocol, ensuring seamless connectivity between myriad devices. However, the complexity of Profinet networks means that troubleshooting is an inevitable necessity. Here, we delve into effective strategies for diagnosing common Profinet issues, alongside a toolkit designed to tackle these challenges head-on.
Unraveling Connectivity Conundrums
At the heart of Profinet troubleshooting is addressing connectivity issues. These often arise from physical layer complications such as malfunctioning cables or incorrect port configurations. A meticulous inspection of cables, connectors, and ports is essential, seeking out any visible signs of wear or disconnection.
Configuration Clarity
Misconfigurations can silently undermine a Profinet network. Ensuring that all devices boast correct IP settings and that there’s harmony in network parameters is crucial. This includes averting the common pitfall of IP conflicts which can disrupt the network flow.
The Traffic and Collision Crossroad
High network traffic and collisions can be the bane of network efficiency, leading to data loss or delays. Monitoring traffic flow and collision rates can offer insights into potential bottlenecks or network inefficiencies.
Device Diagnostics
Modern Profinet devices come equipped with diagnostic capabilities. Leveraging these built-in diagnostics can provide a direct window into device-specific errors, aiding in pinpointing the root cause of issues.
The Profinet Troubleshooting Arsenal
The market offers a plethora of tools designed to ease the Profinet troubleshooting process:
- Wireshark with Profinet plugins: This tool stands out for its ability to dissect Profinet traffic, offering a granular view of data transmission and potential irregularities.
- Manufacturer-specific Diagnostic Software: Many Profinet devices come with proprietary software, rich in diagnostic features that allow for real-time monitoring and error logging.
- Physical Layer Tools: From cable testers to network analysers, these tools are indispensable for identifying and resolving physical connectivity issues.
- Comprehensive Engineering Tools: Platforms like Siemens’ TIA Portal provide a holistic view of the network, including topology visualisation and device management capabilities.
Beyond Basic Troubleshooting
For those seeking to preemptively tackle Profinet challenges, simulation tools offer a sandbox for identifying configuration errors or potential network issues before they escalate. Furthermore, advanced Profinet controllers with diagnostic capabilities can serve as an early warning system, flagging network health issues or maintenance needs.
Cultivating a Profinet-Savvy Environment
Maintaining an up-to-date repository of network documentation and ensuring regular firmware updates are fundamental best practices. Additionally, investing in Profinet-specific training for technical staff can dramatically shorten the time to resolution when issues arise.
Troubleshooting Profinet networks demands a blend of systematic approaches and specialised tools. By adopting a methodical strategy and harnessing the right technological aids, maintaining the health and efficiency of Profinet networks becomes a more manageable endeavour.
In summary, the OSI model’s layered approach provides a structured framework for understanding and designing communication processes within engineering process control systems. It ensures that complex control systems have a standardised method for data exchange, error handling, and system management, contributing to their efficiency, reliability, and security.




